The early signs of a security incident are rarely black-and-white. Most individuals and organisations respond to security incidents in every imaginable way, and it’s always a knee-jerk reaction. To remediate a security incident, a proper incident response plan should be established.
In simple terms, incident response is the process of detecting and analysing incidents and mitigating their impact on an organisation. It’s very pivotal that every organisation should establish and enforce an Incident Response Plan to be implemented by an Incident Response Team.
Frequent attacks compromise the operations of organisations, and it’s imperative that organisations create procedures, policies, and plans to effectively protect against incidents. The goals of an Incident Response Plan should include, but not be limited to:
1. Assert that an incident has occurred
2. Restore business continuity
3. Minimise the impact of the incident
4. Ascertain how the incident occurred
5. Forestall future attacks/incidents
6. Improve the organisation’s security posturing
7. Communicate clearly with management and team members
INCIDENT RESPONSE LIFE CYCLE
An Incident Response Plan, integrated into the Incident Response Lifecycle, offers unique advantages that can significantly mitigate the impact of a breach. From a best-practice standpoint, the IRP Plan should encompass all layers of the lifecycle: preparation, detection & analysis, containment, eradication & recovery, and post-incident activities.
PREPARATION
Preparation is a vital step in incident remediation. Preparation is important for reducing the risk of attacks across an organisation’s systems and applications. The Incident Response personnel should endeavour to keep all tools and resources up to date, and the areas of focus should include network security, risk assessments, malware prevention, and employee awareness.
DETECTION & ANALYSIS
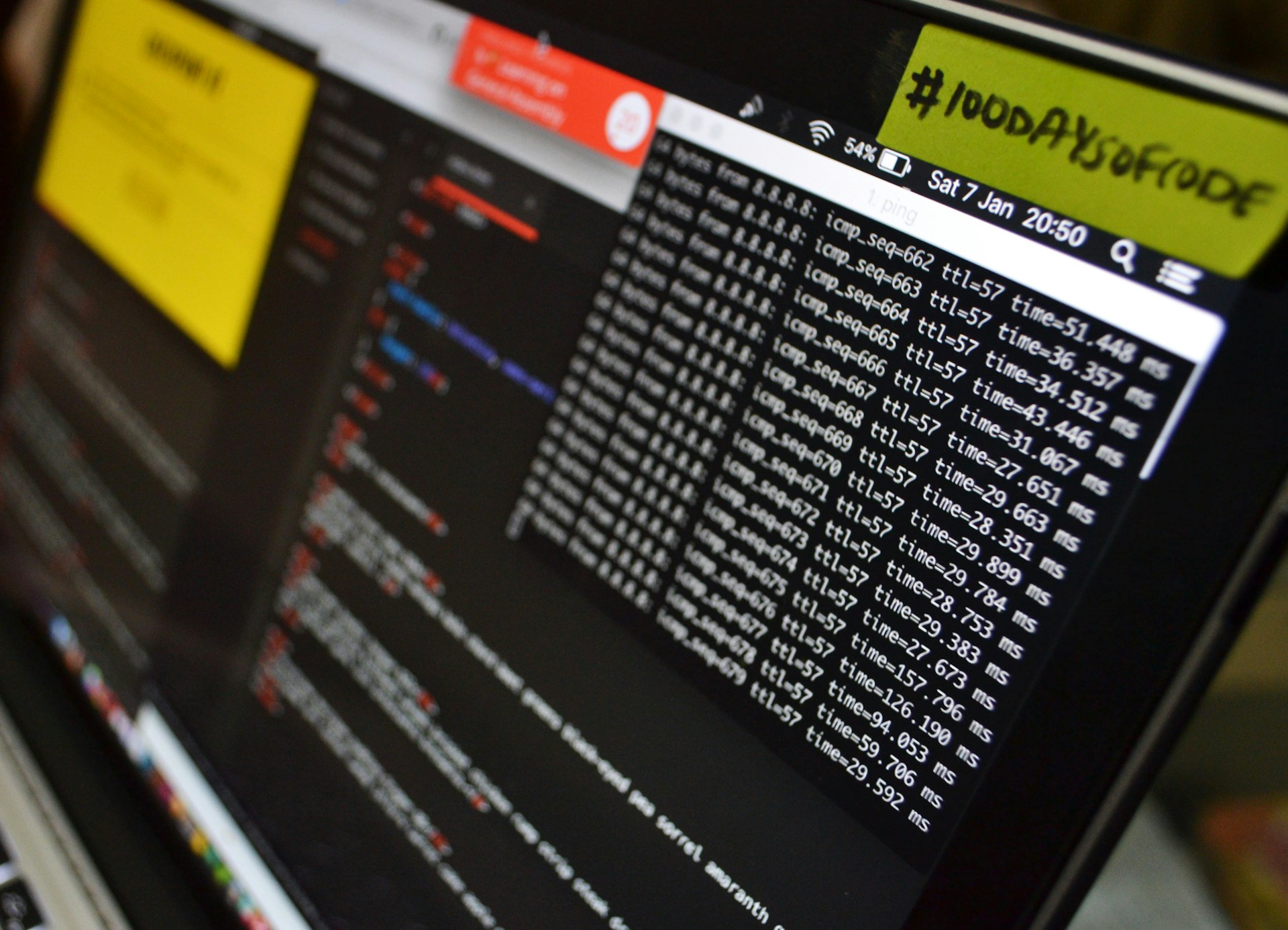
Due to the scale of recent attack vectors, precisely detecting incidents is difficult for most organisations. Currently, there are numerous network security tools, such as Intrusion Protection Systems and Intrusion Detection Systems, that help mitigate attacks. When an incident occurs, Incident Response personnel should analyse and validate it as quickly as possible. The initial analysis should focus on determining the incident’s extent, the affected systems/applications, and how the incident occurred. After the analysis, an indicator must be assigned to prioritise the severity of incidents and their impact on the organisation. Team members must communicate clearly to upper management, and feedback received must be distributed across the board.
CONTAINMENT, ERADICATION & RECOVERY
Containment is of vital importance before an incident permeates throughout an organisation’s network. As a best practice, standards, procedures, and strategies for containment must have been predetermined to facilitate decision-making. The incident handler’s decision-making process is the game-changer in containing threats. Collecting and keeping evidence is also vital if there is a legal basis for the incident. Elimination is also vital to remove components of the incident that could disrupt business continuity, such as malware or compromised accounts. At the end, system administrators restore failed systems, recover them, and, most importantly, remediate vulnerabilities to prevent similar threats from recurring.
POST-INCIDENT ACTIVITY
As soon as organisational processes have been restored and returned to normal, it’s paramount to initiate a knowledge transfer process for the lessons learnt. A full-scale report should be prepared to guide efforts to prevent similar incidents in the future. Incident data collected should be mined for actionable insights, and this could help ascertain costs to the organisation to name a few. Failure to establish an effective Incident Response Plan could leave your organisation vulnerable to cyberattacks, while having the right plan can help mitigate incidents and strengthen your organisation’s security posture.